Introduction
This CTF focuses on subdomain enumeration — a critical reconnaissance technique used to discover hidden services and potential attack vectors. We'll use ffuf for fuzzing and inspect SSL certificates to uncover secrets.
🎯 Skills Covered
Subdomain enumeration, Virtual host fuzzing, SSL certificate inspection, DNS configuration
Subdomain Enumeration
First, let's enumerate subdomains using ffuf (Fuzz Faster U Fool). We'll use a wordlist to brute-force potential subdomains:
ffuf -u https://10.49.129.85 -w /usr/share/seclists/Discovery/DNS/subdomains-top1million-5000.txt -H 'Host: FUZZ.futurevera.thm' -fs 4605Breaking down this command:
-u— Target URL-w— Wordlist for fuzzing-H 'Host: FUZZ.futurevera.thm'— Fuzzes the Host header (virtual host enumeration)-fs 4605— Filter out responses of size 4605 (default page)
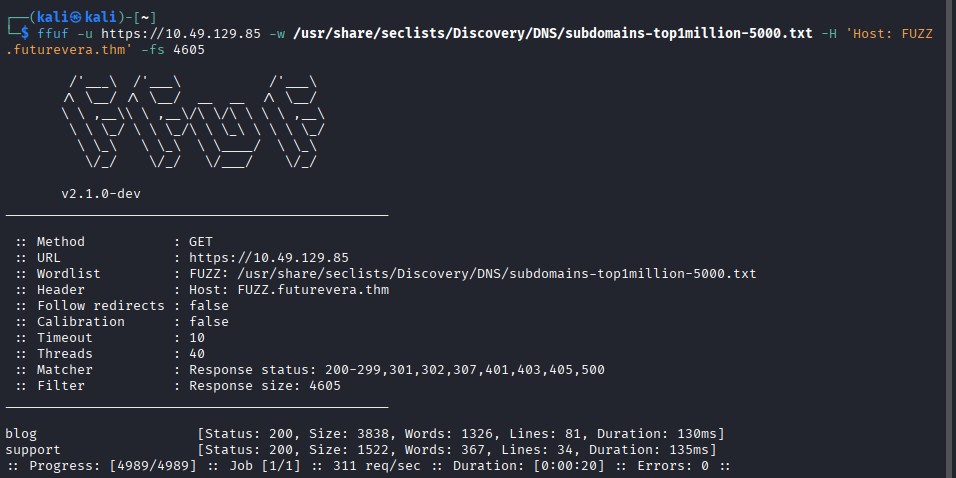
ffuf discovering subdomains: blog and support
Two subdomains were identified:
- blog.futurevera.thm
- support.futurevera.thm
Certificate Inspection
When visiting support.futurevera.thm, let's inspect the SSL certificate for additional information. Click on the padlock icon and view the certificate details.
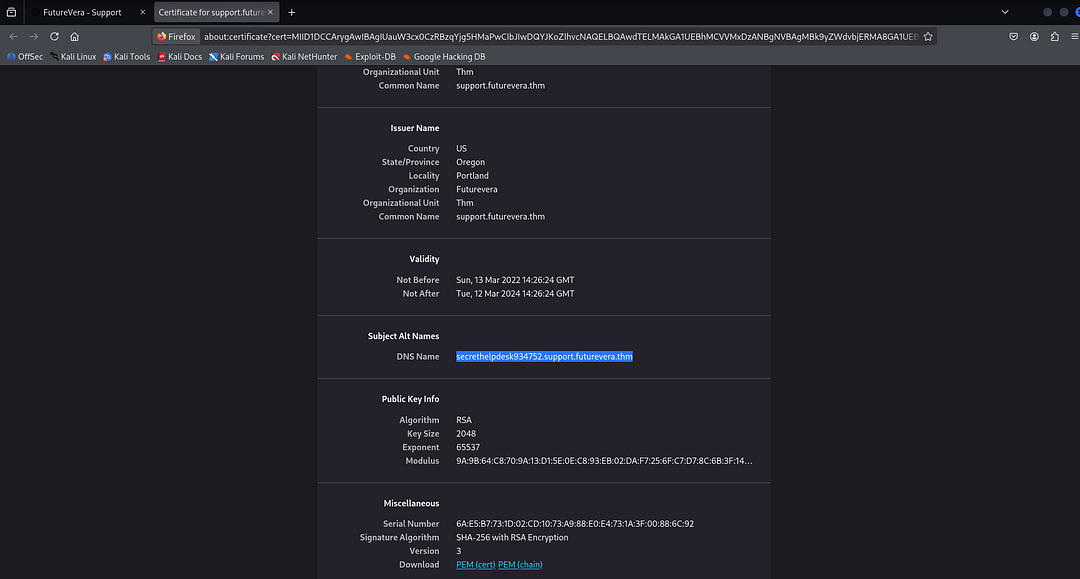
Certificate reveals a hidden subdomain in Subject Alt Names
In the Subject Alt Names section, we discover a hidden subdomain:
secrethelpdesk934752.support.futurevera.thm💡 Pro Tip
Always inspect SSL certificates! They often contain additional DNS names in the Subject Alternative Name (SAN) field that aren't publicly advertised.
Accessing the Hidden Subdomain
Add the discovered subdomain to your /etc/hosts file:
sudo nano /etc/hosts
# Add this line:
10.49.129.85 secrethelpdesk934752.support.futurevera.thmNow navigate to the hidden subdomain:
http://secrethelpdesk934752.support.futurevera.thm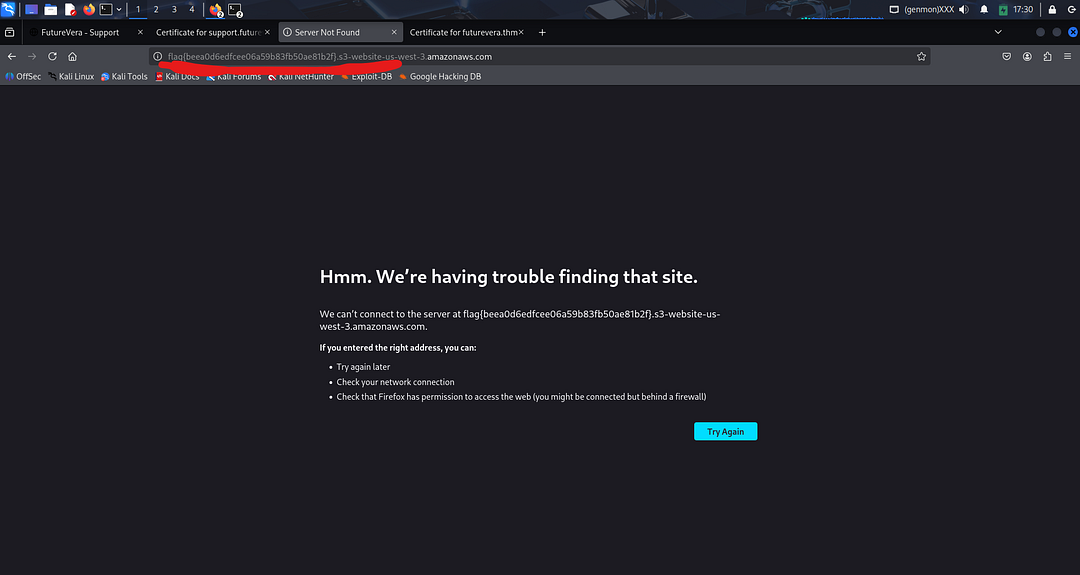
The flag is revealed in the URL!
🚩 Flag Captured!
flag{beea0d6edfcee06a59b83fb50ae81b2f}
Attack Summary
Subdomain Fuzzing
Used ffuf to discover blog and support subdomains via virtual host enumeration
Certificate Inspection
Examined SSL certificate and found hidden subdomain in Subject Alt Names
DNS Configuration
Added the secret subdomain to /etc/hosts
Flag Capture
Accessed the hidden subdomain and captured the flag
Key Takeaways
🔑 Lessons Learned
- Enumerate subdomains — Hidden services often run on subdomains
- Inspect certificates — SAN fields can reveal internal hostnames
- Virtual host fuzzing — Multiple sites can share the same IP
- Always check thoroughly — The obvious paths aren't always the answer
Thanks for reading! 🎉